08 Mar Pentest Glory: Spearfish, S.D. Woman Duped Prison Authorities
John Strand’s mom spent a day in the big house
Melbourne, Australia – Mar. 8, 2021
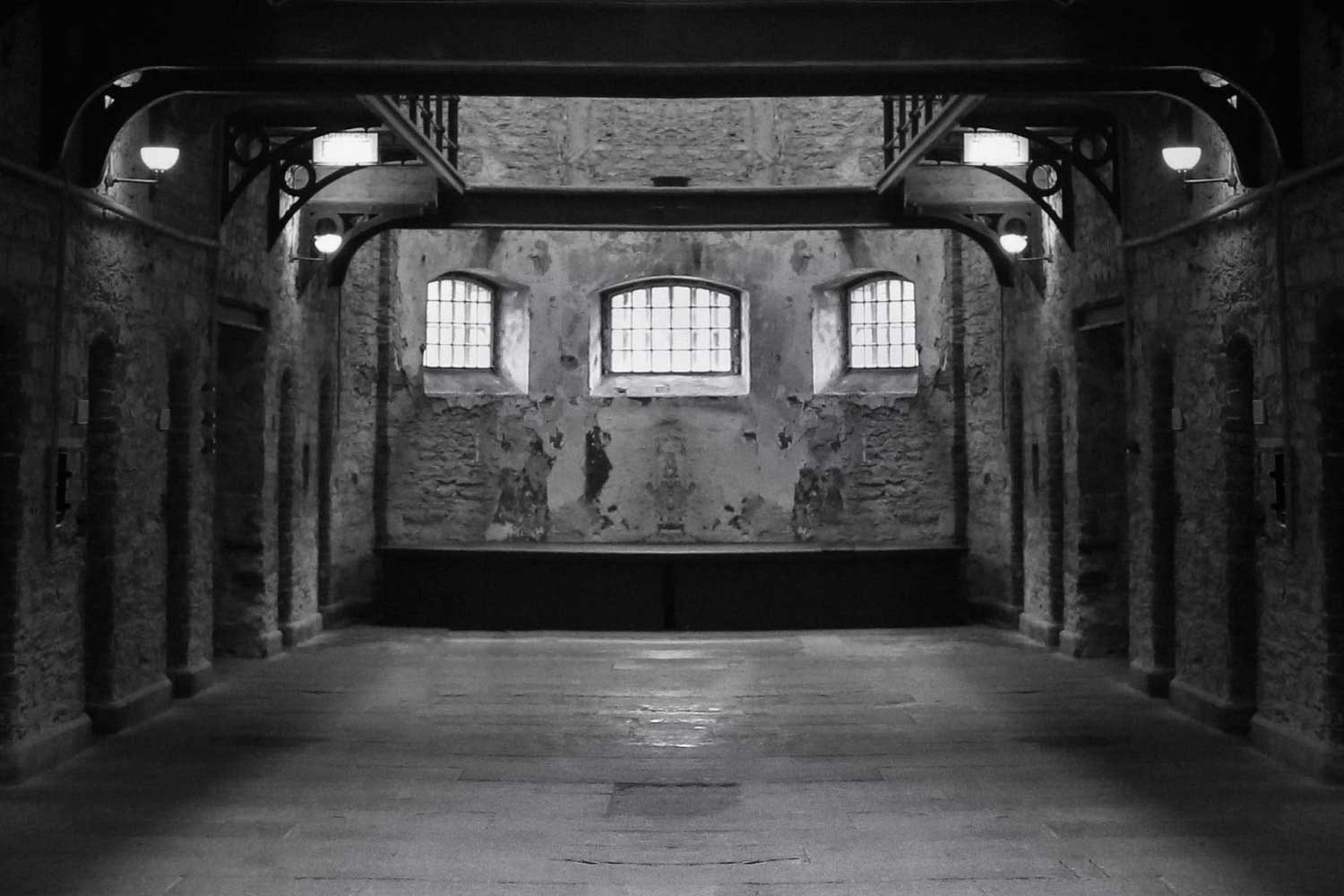
Security specialist John Strand has been teaching companies how to do successful penetration testing for years, but it was his mom who ended up being blacklisted after she successfully duped prison authorities — walking into a South Dakota prison in a ruse that she talked about with pride for the rest of her life.
Having helped her son manage the business side of Black Hills Information Security — based out of the appropriately-named town of Spearfish, South Dakota — Strand’s mom became interested in the security testing work that he and his team of two dozen security specialists conduct on a regular basis.
Noting that they were scheduled to conduct a series of physical penetration tests, she volunteered to try one herself — setting herself up in the guise of a food safety inspector, something she knew from decades of experience in her past career.
“She was already reading about these cool things we were doing, breaking into various places,” Strand told Cybercrime Magazine, “and we were sitting around the dinner table when she said, ‘I would really like to try that’.”
Although she stocked up on clipboards, state health inspection sheets, food thermometers and the like, it wasn’t until she jumped into her car and disappeared that what she was doing began to sink in.
Cybercrime Radio: John Strand Shares A Penetration Testing Classic
How My Mom Broke Into A Prison
“I was thinking that this might not be a really great idea at all,” he recalled. “She was gone for about half an hour and we had no indication whether or not she was OK, or she was arrested, or anything.”
Then, he said, the beacons — malware-like code on a USB stick that “phones home” to let the team know that a target system has been successfully breached — started to appear in a clear sign that his mom had not only not been arrested, but was succeeding.
It turned out, she said in recounting her adventure later on, that the prison authorities had been exceedingly helpful — offering to show her anything she needed to see and giving her “pretty much free rein” to walk into the employee café, food preparation areas, and even the network operations center (NOC).
“She was walking around plugging in USB sticks and getting the callbacks,” he laughed, “but she gave them a full health inspection, with a score and everything.”
When Mrs. Strand was finished, the prison director called her into her office and asked whether there were any self-assessment documents that the prison could use; without pausing, Strand’s mom gave the director a USB stick that gave the Black Hills team direct access to the director’s system as well.
Stay in your lane
The story is good for a laugh now, but Strand later found out that his mom was “absolutely terrified” throughout the drill.
Still, she stayed in her role and completed a penetration test so successful that some new Black Hills clients insisted on having a clause in their contract explicitly banning Strand’s mom from conducting a penetration test.
Ultimately, he said, the story is a stark reminder of how easily people — even people who should know better, like prison authorities — can be deceived by “perceived authority.”
“Whenever you talk to people that are trying to do physical pen tests,” he explained, “the best thing you can do is do what you know. And my mom had been a food service director for 25 years in the school system, so she knew this inside out and backwards — and had absolute authority in that role.”
Presented correctly, that authority can override any amount of training or common sense that people have — and it doesn’t take impersonating a police officer (a no-go area for pen testers) to make it happen.
Strand has seen it time and again over the years, sharing stories of procedural vulnerabilities that often see “people get bent out of shape.”
“They get nervous and they’re saying ‘that’s really dangerous’,” he said, giving the example of paycheck companies where his team has been able to call up, impersonate an employee, and talk their way to getting system access that lets them do things like adding new employees or changing salaries.
Many companies put constraints around their pen-testing activities due to particular sensitivities around their business activities — but this reflects a belief that “hiding our head in the sand is better than actually exposing these specific weaknesses as they exist.”
Yet it’s not just the clients that need to become more accepting of penetration testing; citing cases where penetration testers have inadvertently summoned the police with sirens blazing, Strand — who contributes to the Penetration Testing Execution Standard — admits the industry also needs “better coordination, between security and especially law enforcement” to avoid causing panic.
“What we do in pen testing sounds really scary,” Strand said. “We rob banks for a living, we break into universities, we steal secrets — and the idea that that activity can be not just legal, but essential to security, is something that’s very difficult for people to understand.”
Reaching out to communities and communicating with people “was really a good first step,” he said, noting that greater collaboration will help build broader support for pen-testing as a critical security function.
“Unfortunately, there are still areas in computer security that are like sacred cows, that you’re not allowed to interact with or touch,” he said. “And those tend to be some of the most fragile areas that need breaking — to implement better security policies.”
– David Braue is an award-winning technology writer based in Melbourne, Australia.
Go here to read all of David’s Cybercrime Magazine articles.


 –
– 