30 Nov Boardroom Cybersecurity Report 2023
Cybercrime facts, figures, predictions, and statistics for C-Suite executives. Sponsored by Secureworks
Sausalito, Calif. – Dec. 13, 2023 / Press Release
Cybercrime is predicted to cost the world $9.5 trillion USD in 2024, according to Cybersecurity Ventures. If it were measured as a country, then cybercrime would be the world’s third-largest economy after the U.S. and China.
We expect global cybercrime damage costs to grow by 15 percent per year over the next two years, reaching $10.5 trillion USD annually by 2025, up from $3 trillion USD in 2015. This represents the greatest transfer of economic wealth in history, risks the incentives for innovation and investment, is exponentially larger than the damage inflicted from natural disasters in a year, and will be more profitable than the global trade of all major illegal drugs combined.
The damage cost estimation is based on historical cybercrime figures including recent year-over-year growth, a dramatic increase in hostile nation-state-sponsored and organized crime gang hacking activities, and a cyberattack surface which will be an order of magnitude greater in 2025 than it is today.
Cybercrime costs include damage and destruction of data, stolen money, lost productivity, theft of intellectual property, theft of personal and financial data, embezzlement, fraud, post-attack disruption to the normal course of business, forensic investigation, restoration and deletion of hacked data and systems, reputational harm, legal costs, and potentially, regulatory fines.
“Unfortunately, most organizations are more vulnerable than they realize,” says Wendy Thomas, CEO at Secureworks, on the Bloomberg Businessweek Podcast. “It may be that they’ve done a great job of protecting their own assets but they are inextricably linked with other vendors, other suppliers. Thinking about your security as having to secure those who are interoperating with your organization and your systems as much as you secure your own castle is probably the most important.”
“We’re tracking about 135 active threat groups, and their activities are bucketed primarily into traditional cybercrime, just looking to extract profits; nation-state activity, which is clearly up in the wake of geopolitical events; and then hacktivists, who are concerned about those events and making their voice heard through a variety of cyberattacks,” adds Thomas. “In terms of nation-state actors and cybercrime groups, we see those coming out of China and Russia primarily, respectively, but certainly Iran, North Korea, and others are active on the cyber stage.”
BACK TO THE FUTURE
The chief information security officer (CISO) role dates back to 1994 when financial services giant Citigroup (then Citicorp, ranked 17th on the Fortune 500 at the time) established a specialized cybersecurity office after suffering a series of cyberattacks from Russian hackers.
Steve Katz was anointed CISO.
“I was running information security at JPMorgan at the time, and the rumor on Wall Street was that Citicorp had been hacked,” recalled Katz, in an interview with Cybersecurity Ventures.
“You know we had the hack so you have a blank check to set up anything you want,” Katz was told by his new bosses, who were tapped by the CEO and board at Citicorp to shore up their digital defenses.
“We want to make sure it doesn’t happen again. We want you to build the best information security department anywhere on the globe.”
Cybercrime Radio: Back To The Future
World’s first chief information security officer
Katz traveled the globe as Citi’s ambassador, set on regaining the trust of the bank’s most important clients. He also built an exceptional team, an important request from the board.
Fast-forward nearly three decades and today’s boards and CEOs aren’t nearly as involved with cybersecurity as Citi was when the world’s first CISO was hired.
All too often it’s not until an organization suffers a cyberattack that the board gets involved. And by that time, money isn’t going to solve the problem.
“The reality is that business executives can’t outspend the (cybersecurity) issue and they must be prepared,” says Theresa Payton, former CIO at The White House and a top global cybersecurity expert who routinely advises boardroom and C-suite executives.
“Cybersecurity no longer exists in a vacuum,” adds Payton, “and it must be elevated to the conversations held in the boardroom and with senior leadership as entire divisions, departments, and organizations. Cybersecurity is a team sport. We’re all responsible.”
It’s time for boardroom and C-suite executives to join the discussion deciding the future of cybersecurity, and to take charge of defending their businesses.
CYBER STATISTICS
“The average cost of a breach for a business in the U.S. to date this year is nearly $10 million dollars a piece,” says Secureworks’ Thomas. “The global cost of cybercrime is expected to be 3x what it was just a decade ago. We’re talking about a transfer of wealth in the wrong direction that’s probably the greatest in our history.”
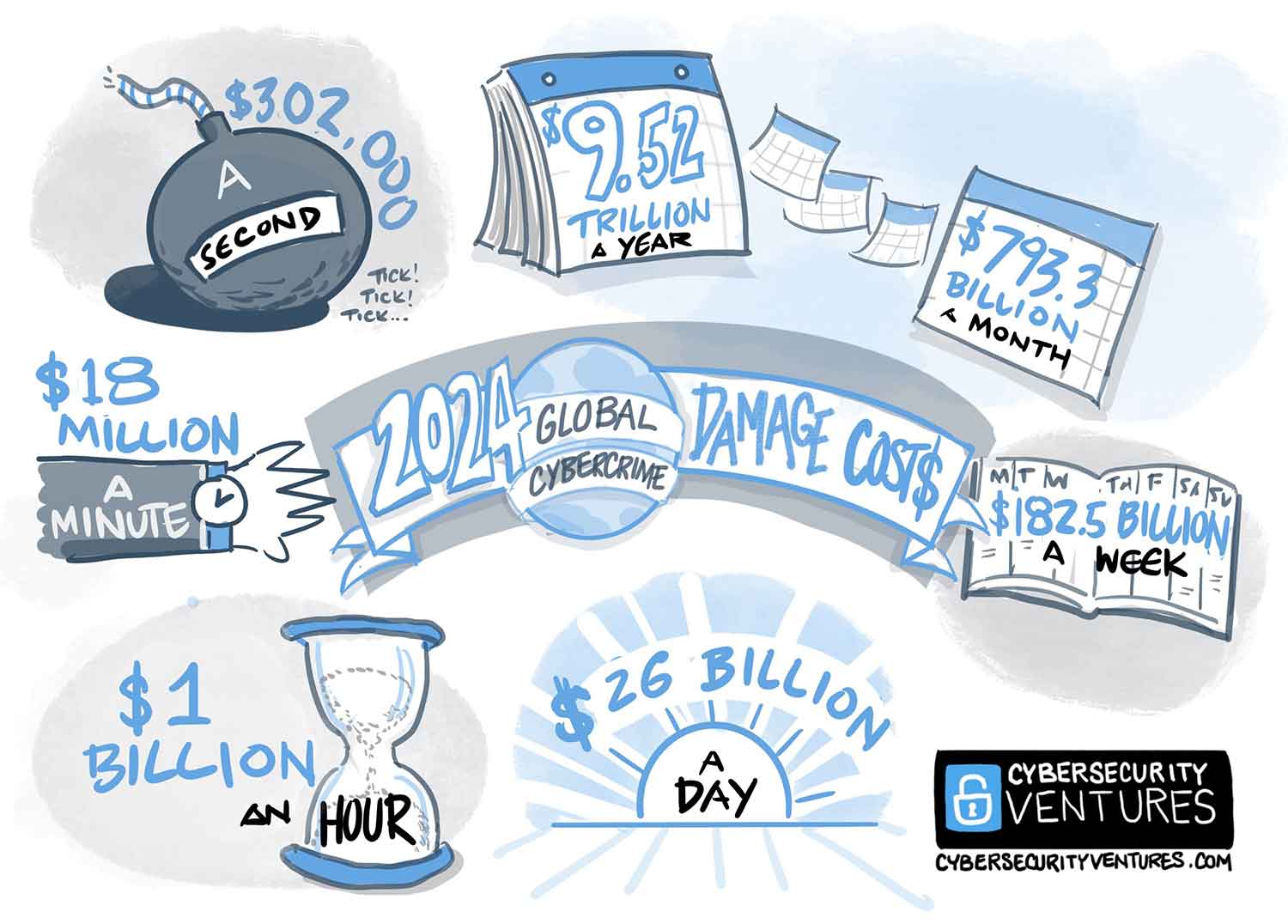
- In 2024, cybercrime is predicted to cost the world $9.5 trillion, which breaks down to: $793 billion USD a month; $182.5 billion USD a week; $26 billion USD a day; $1 billion USD an hour; $18 million USD a minute; $302,000 USD a second.
- Ransomware will cost its victims approximately $265 billion USD annually by 2031, Cybersecurity Ventures predicts, with a new attack taking place on consumers and organizations every two seconds. This is up from $20 billion USD in damages and an attack every 11 seconds in 2021.
- Rapid growth in the use of decentralized finance (DeFi) services is creating a new soft spot for global financial systems, fostering new methods of cryptocrime for cybercriminals whose “rug pulls” and other attacks will, Cybersecurity Ventures predicts, cost the world $30 billion in 2025 alone. That’s nearly twice the $17.5 billion lost in 2021 — and expected to grow by 15 percent annually as the cryptocurrency market continues to expand.
- Cybercrime will propel global spending on cybersecurity products and services to $1.75 trillion USD, cumulatively, for the five-year period from 2021 to 2025, according to Cybersecurity Ventures. We predict expenditures for cybersecurity products and services globally will grow to nearly $459 billion USD on an annual basis in 2025.
- Cybersecurity Ventures predicts the cyberinsurance market will grow from approximately $8.5 billion USD in 2021 to $14.8 billion in 2025, and will exceed $34 billion USD by 2031, based on a compound annual growth rate (CAGR) of 15 percent over an 11-year period (2020 to 2031).
- The number of unfilled cybersecurity jobs worldwide grew 350 percent between 2013 and 2021, from 1 million to 5 million, according to Cybersecurity Ventures. We predict that in five years from now, the same number of jobs will remain open.
- We estimate the world will need to secure 338 billion lines of new software code in 2025, up from 111 billion lines of new code in 2017, based on 15 percent year-over-year growth in new code.
- Cybersecurity Ventures predicts that total global data storage will exceed 200 zettabytes by 2025. This includes data stored on private and public IT infrastructures, on utility infrastructures, on private and public cloud data centers, on personal computing devices — PCs, laptops, tablets, and smartphones — and on IoT (Internet-of-Things) devices.
- The total amount of data stored in the cloud — which includes public clouds operated by vendors and social media companies (think Apple, Facebook, Google, Microsoft, X, etc.), government-owned clouds that are accessible to citizens and businesses, private clouds owned by mid-to-large-sized corporations, and cloud storage providers — will reach 100 zettabytes by 2025, or 50 percent of the world’s data at that time, up from approximately 25 percent stored in the cloud in 2015.
- Roughly one million more people join the internet every day. There were around 6 billion people connected to the internet interacting with data in 2022, up from 5 billion in 2020 — and more than 5 billion internet users in 2030. If street crime grows in relation to population growth, so will cybercrime.
CYBERSECURITY IN THE BOARDROOM
To mitigate the cyber threat, cybersecurity should be a high priority in the boardroom of every company.
However, according to the 2023 Heidrick & Struggles Board Monitor Report, last year only 14 percent of non-executive director appointments at the largest publicly listed companies were issued to those with some level of cybersecurity acumen, a decline from 17 percent for the year prior.
For several years, the Federal Trade Commission (FTC) has urged the enterprise, and their boards, to take a stronger stance on cybersecurity. The SEC has also recently adopted new rules that require U.S. public companies to disclose “material” cybersecurity incidents and to report on their approach to cybersecurity risk management, strategy, and governance on an annual basis.
It is crucial that CEOs and security leaders are on the same page in regard to securing their own companies. There does appear, however, to be a disconnect between the expected levels of cybersecurity awareness in the executive space, education, and how leadership wishes to respond to incidents.
After all, executives and board members often have differing priorities and speak in different languages. Cybersecurity initiatives can sometimes be seen as growth restrictors and barriers to efficiency and productivity, but boards need to recognize that reducing threat risk is an advantage, not only to the business at hand but also to themselves.
Cybercrime Radio: Cybersecurity Advice for CEOs
A lot of accountability and regulation on the way
Executives and leaders are now often held culpable — at least, publicly — when a significant cybercrime occurs, and if Gartner is to be believed, then 75 percent of CEOs may be found personally liable for cyber-physical incidents by 2024.
The recent sentencing of former Uber security chief Joseph Sullivan to serve a three-year probationary term for attempting to cover up a data breach had the ripple effect of CISOs fearing future scapegoating.
The U.S. Department of Justice (DoJ) is now urging security leaders to continue working with law enforcement, despite such concerns.
“This intentional activity, misleading the FTC, has nothing to do with the well-meaning and stressful work that CISOs and compliance officers have to deal with in the heat of the worst day of their lives if they’re undergoing a breach,” said Deputy Attorney General Lisa Monaco in relation to the case.
The Securities and Exchange Commission (SEC) recently announced charges against Austin, Texas-based software company SolarWinds Corporation and its chief information security officer, Timothy G. Brown, for fraud and internal control failures relating to allegedly known cybersecurity risks and vulnerabilities.
On a positive note, and a sign of progress, Cybersecurity Ventures predicts that by 2025, 35 percent of Fortune 500 companies will have board members with cybersecurity experience, and by 2031 that will climb to more than 50 percent. This is up from an estimate of 17 percent in 2021.
RANSOMWARE
A 2017 report from Cybersecurity Ventures predicted ransomware damages would cost the world $5 billion USD in 2017, up from $325 million USD in 2015 — a 15 times increase in just two years. The damages for 2018 were predicted to reach $8 billion USD, for 2019 the figure was $11.5 billion USD, and in 2021 it was $20 billion USD — 57 times more than in 2015.
Ransomware costs are now expected to exceed $265 billion USD annually by 2031, Cybersecurity Ventures predicts, with a new attack (on consumers and organizations) every 2 seconds as ransomware perpetrators progressively refine their malware payloads and related extortion activities. The dollar figure is based on 30 percent year-over-year growth in damage costs over the next 10 years.
At present, the largest ransomware payout was made by CNA Financial, that of $40 million USD to the Russian ransomware gang Phoenix.
Furthermore, the government intends to launch a new U.S. federal program to warn American companies when they are vulnerable to ransomware attacks.
Cybercrime Radio: The Ransomware Plague
All industries are at major risk
The White House now deems ransomware a “threat to national security, public safety, and economic prosperity,” and as part of a new security strategy, software developers may be held liable for vulnerabilities. Federal grant issuance could also be based, in part, on an applicant organization’s security posture.
“We are denying our adversaries access to technical infrastructure and cutting off their funding. We’re disrupting the criminal ecosystem by making cybercrime and ransomware less lucrative and higher risk. We are helping the private sector defend itself more effectively with key intelligence and threat information,” said Matthew Olsen, U.S. Assistant Attorney General, in a recent speech.
According to the World Economic Forum’s annual report, “The Global Cybersecurity Outlook 2023,” when asked what cyber risk security leaders and business leaders were most concerned about when it comes to personal cybersecurity, both cited identity theft as their main concern, followed by cyber extortion and ransomware.
These concerns ranked higher than personal financial losses, critical infrastructure breakdown, geopolitical instability, and cyber warfare.
There is also the prospect of insider threats to consider. Insider threats can be accidental or deliberate, but with the global economy in dire straits, increased cost of living and job insecurity may have a psychological impact that would turn otherwise loyal employees.
A 2022 poll of IT and security leaders indicates that 65 percent of respondents said they, and their employees, had been approached to act as insiders for ransomware attacks, with payment made in cash or Bitcoin.
Today’s business leaders know that ransomware can grind their operations to a halt. However, tackling ransomware by building resiliency programs, training, adopting robust security policies, and investing in the right security solutions are defensive measures that may work now — but they must constantly be audited, updated, and adapted to handle a threat expected to plague us for years to come.
After all, cyberattackers only have to succeed once to deal severe damage to an organization’s infrastructure and balance sheet.
Ransomware is clearly a discussion topic for the boardroom. But is it being raised before or after your organization is struck?
CRYPTOCRIME
Loose regulations, a lack of governance, and rapid growth in decentralized finance (DeFi) services are creating weak spots in global financial systems, fostering new methods of cryptocurrency-related crime. Cybercriminals, long associated with rug-pulls, exit scams and investment fraud schemes will, Cybersecurity Ventures predicts, cost the world an estimated $30 billion USD annually by 2025.
Losses are expected to grow by 15 percent annually.
It is important to know that cryptocrime is uniquely different from other types of cybercrime, and cybercriminal attention to cryptocurrency manifests itself in numerous ways.
Cryptocurrencies are not typically backed by central financial systems or governments, and even when their value is linked to fiat currency — such as the U.S. dollar — there is no guarantee of a sound investment.
While cryptocurrencies originated as a way to free up finance from centralization, cryptocurrencies — including Bitcoin (BTC) and Ethereum (ETH) — held in digital wallets, can also be abused for criminal purposes, such as illicit transfers and money laundering, which are easier to accomplish than through traditional financial systems.
Cybercrime Radio: Cryptocrime surging
Second fastest growing type of cybercrime
The FBI’s Internet Crime Complaint Center (IC3) says that the majority of investment fraud cases reported involved cryptocurrency. In 2022, losses increased by 183 percent from 2021 to $2.57 billion USD.
While Chainalysis mid-year estimates (as of Jun. 30, 2023) suggest that overall cryptocurrency-related crime and illicit transaction volumes are decreasing compared to 2022, ransomware-related crime has surged due to big game hunting.
The blockchain, the underlying infrastructure of decentralized technologies including cryptocurrency exchanges, is a relatively new technology. Its implementations and adjacent processes are fraught with cybersecurity challenges.
Cybercriminals know it.
Hacks related to DeFi and cryptocurrency-related blockchains, including Curve Finance liquidity pools being exploited to the tune of $70 million USD, Atomic Wallet’s wallet exploit causing over $100 million USD in losses, and Binance’s smart contract bug leading to the theft of over $500 million USD, have collectively totaled hundreds of millions of dollars in monetary losses and related damages.
In response, the U.S. government established the National Cryptocurrency Enforcement Team (NCET) in 2022. The new branch has proven to be successful, with a number of cryptocurrency crime-related prosecutions under its belt.
In 2023, NCET merged with the Computer Crime and Intellectual Property Section (CCIPS), ensuring its permanency as a federal investigation unit.
While commodities fraud, exit scams, and market manipulation are all on the CCIPS radar, so is ransomware — as cryptocurrencies tend to be the currency of choice in extortion.
“Ransomware is a threat to all — national security, public safety, and economic prosperity,” says Nicole Argentieri, U.S. Principal Deputy Assistant Attorney General.
“Deputy Attorney General Monaco described what we are up against perfectly when she referred to it as a ‘blended threat.’ Some national security threats come from nations. Some come from ‘nation-states and criminal gangs forming alliances of convenience and working together.’ And some come from criminal groups working alone and the disastrous consequences of their hacks.”
Does your board have a go-to cryptocrime or cryptosecurity expert?
CYBERSECURITY SPENDING
Buoyed by the need to execute digital transformation initiatives faster than ever, with the pandemic having a cataclysmic impact on business operations, organizations in their droves have adopted cloud and virtual tools, rapidly increasing the potential attack surface.
Yet even as these services took center stage in company transformations, they also became attractive to cybercriminals seeking ways to exploit weaknesses and blind spots in newly introduced systems, alongside the often unwitting threat posed by remote workers.
Cisco’s Cybersecurity Readiness Index indicates that only 15 percent of organizations have reached the “mature” level necessary to successfully fend off modern cyberthreats.
Furthermore, 60 percent of private sector cybersecurity leaders responding to Cisco’s survey said they had experienced a cybersecurity incident in the last 12 months. In total, 41 percent of those impacted disclosed costs of at least $500,000 USD.
Little wonder that CEOs now identify cybersecurity as one of the most significant risks their businesses face. While other technology sectors are driven by reducing inefficiencies and increasing productivity, cybersecurity spending is driven by cybercriminal activity.
Cybercrime Radio: CISOs in the Boardroom
Most F500 co’s don’t have cyber experience on their board
Cybercrime and the need to protect networks increasing in complexity – including Internet of Things (IoT) devices, remote privileged access, vast troves of data, and numerous endpoints – will propel global spending on cybersecurity products and services to $1.75 trillion USD, cumulatively, for the five-year period from 2021 to 2025, according to Cybersecurity Ventures.
We predict expenditures for cybersecurity products and services globally will grow to nearly $459 billion USD on an annual basis by 2025.
“Your security budget ultimately depends on the ‘crown jewels’ you need to protect, says Scott Schober, author of the popular book “Hacked Again” and chief security officer at Cybersecurity Ventures. “That’s different for every organization — but you can’t rightsize your budget until you clearly understand exactly what you need to protect, the level of risk you face, and the measures you therefore need to implement to achieve your risk-reduction goals.”
As we know, many security incidents are due to the human factor. Layered security and robust endpoint and network protection cannot be managed by tools and technology alone — employees must also have a solid level of cyber awareness to avoid falling prey to phishing scams, which are one of the main reasons why organizations are compromised.
Cybersecurity Ventures predicts that global spending on security awareness training for employees will exceed $10 billion USD by 2027, an increase from approximately $5.6 billion USD in 2023.
What business isn’t going to do and spend whatever it takes to recover from being hacked?
Cybersecurity theoretically has no spending limit. There is a budget before a company suffers a cyberattack or a series of them, and then there’s the actual spending that takes place afterward.
Members of the board also have to consider how budgets are best spent. Security solutions, especially those implementing new detection technologies enhanced by artificial intelligence (AI) and machine learning (ML) are important, but executives will also want to avoid waste — spending money on numerous tools that only accumulate over time, cause overlaps, and provide no real intrinsic value.
“When we talk to CEOs and CIOs about protecting their organizations, it really is all about time — time to detect, time to respond — and that’s where the power of artificial intelligence really comes into play to turn that back against the adversary,” says Secureworks’ Thomas.
As humans are the first line of defense, investments in new technological solutions should support employees, improve their awareness, and augment them to be security-first in their roles without hampering productivity.
A boardroom sanity check on a realistic cybersecurity budget should also take unexpected cyberattacks into consideration.
The cost of falling victim to a cyber or ransomware attack can be exponentially greater than the cost of investing in the people and technology that can prevent incidents in the first place — and this is not something the boardroom should realize when it’s too late.
CYBERINSURANCE
Cyberinsurance has evolved rapidly in recent years, driven by the growing threat of cybersecurity compromise and awareness of corporate responsibility around breach prevention.
Yet, as the market’s natural growth continues to be distorted by its untenable exposure to large ransomware payouts — and executive concerns over personal liability — changes to its operation and risk parameters will drive fundamental change through every aspect of the market.
For all its benefits in supporting a business response to conventional data breaches, including accidental data loss caused by employee mishaps, the cyberinsurance industry is still far from resolving its increasingly enmeshed relationship with ransomware.
The issue, of course, revolves around the payment of ransoms — a contentious topic that may, depending on where your business operates, range from perfectly acceptable, to inadvisable, to illegal.
Indeed, the U.S. government is considering an outright ban on ransomware blackmail payments, except in extreme circumstances such as when ransomware prevents critical services from operating.
With Ransomware-as-a-Service (RaaS) catering to a new breed of cybercriminals who do not need technical expertise to launch an attack — instead, they just must have the means to pay for a subscription to ransomware — organizations are at more risk than ever of compromise.
Ransomware gangs now routinely demand millions of dollars and will go so far as to search for revenue and insurance documents once they infiltrate a network to ascertain how much their victim is able to pay.
Cyberinsurers have been forced to respond, and quickly, to lower their exposure to ransomware payouts. Since insurers aren’t generally keen on going bankrupt on behalf of criminals, increasing ransomware payments have driven a rapid surge in cyberinsurance premiums.
Some insurers now also place the onus on insured companies to provide evidence of their efforts to avoid ransomware compromise, on pain of having a claim rejected.
According to Marsh’s U.S. Cyber Purchasing Trends report, companies with greater than $1 billion USD in annual revenues were, by far, the most likely to purchase cyber insurance than smaller firms, at 47 percent and 37 percent, respectively.
Ransomware-related claims alone rose 77 percent in the first quarter of 2023 compared to Q4 2022.
Furthermore, 63 percent of executives surveyed for the report view cyberinsurance as a “key piece of cyber risk management strategy.”
Cybersecurity Ventures predicts the cyberinsurance market will grow from approximately $8.5 billion USD in 2021 to $14.8 billion in 2025, and exceed $34 billion USD by 2031, based on a compound annual growth rate (CAGR) of 15 percent over an 11-year period (2020 to 2031).
Personal liability for cybersecurity incidents is also an emerging issue. Speaking to The Wall Street Journal, Michael Piacente, managing partner at Hitch Partners, said that almost all CISO candidates ask to be under an organization’s insurance policy. Approximately 42 percent of publicly traded companies agree to add their security leaders to policies protecting them from personal losses if they are sued due to decisions made during their tenure.
With this information in mind, a board should scrutinize its cyberinsurance policies and be vigilant in investigating what the market has to offer — as well as account for any reasonable steps cyberinsurers expect organizations to make to avoid a successful attack in the first place.
CYBER FIGHTERS
The need for cybersecurity professionals has been growing rapidly, even faster than companies can hire — and that demand is expected to continue.
The number of unfilled cybersecurity jobs worldwide grew 350 percent between 2013 and 2021, from 1 million to 3.5 million open roles, according to Cybersecurity Ventures. That figure has remained steady and we predict the same number openings through at least 2025.
The U.S. Bureau of Labor Statistics projects that the employment of “information security analysts,” including cybersecurity professionals, will experience a growth rate of 35 percent between 2021 and 2031, compared to an average growth rate of 5 percent for other occupations.
Camille Stewart Gloster, the U.S. deputy national cyber director for technology and ecosystem security, considers filling open cybersecurity roles as a “national security imperative, an economic imperative, a human security imperative.”
However, despite industry efforts to reduce the skills gap, the number of open jobs in our field is still enough to fill 50 NFL stadiums.
CISOs and security leaders are well aware of the labor crunch and ramifications but what about boardroom and C-suite executives?
The more time an organization’s board and C-suite executives spend with its CISO, the more informed they will be.
According to Deloitte’s 2023 Global Future of Cyber Survey, 48 percent of boards in organizations with higher levels of cyber maturity address cyber-related issues quarterly, with 26 percent of survey respondents saying that cyber issues are discussed monthly. In comparison, 59 percent of low cyber performance board members address cyber issues on a monthly basis — but 15 percent also report that discussions only take place twice a year.
Rich Baich, SVP and CISO at AT&T, who previously served as CISO at AIG and Wells Fargo, told Cybersecurity Ventures that boards should be hearing from their CISOs minimally annually but oftentimes quarterly.
“The board should have an educational meeting annually where the CISO provides them with an understanding of the threat, an understanding of what has changed in the environment… really a general understanding of (their) information security,” says Baich.
“The most important thing is truth. How do you get truth to the board?”
Truth be told, most organizations are at risk, in part, because recruiting and retaining cybersecurity professionals is a daunting challenge. This is true of the CISO role.
Cybersecurity Ventures previously found that 24 percent of Fortune 500 CISOs worked in their roles for just one year, on average.
According to a survey of 1,600 CISOs worldwide, 60 percent say they have experienced burnout in the past year, rising to 73 percent of security leaders in the United States.
Gartner predicts that by 2025, 50 percent of cybersecurity leaders will have tried, albeit without success, to use cyber risk quantification to drive enterprise decision-making. In total, only 36 percent of security leaders have managed to achieve action-based results, including cutting costs, reducing risk, or having what the research firm calls “actual decision influence.”
The job is challenging, stressful, and responsibilities shift depending on the company and industry, and so it is unsurprising that so many have a short tenure. After all, in many cases, CISOs are only remembered for the time a security incident has occurred, rather than the times they have been prevented.
C-suite executives should be planning for the inevitable turnover of their CISO.
This is highlighted by the Heidrick & Struggles 2023 Global Chief Information Security Officer (CISO) Survey, in which 41 percent of respondents said their company does not have a succession plan in place — and 13 percent added that their organization is not in the process of developing one.
Board members should also consider ways to improve retention, such as by giving their security leaders the budget and tools they need to perform their jobs correctly — and most importantly, by providing support.
BOARDROOM ACTION
“Boards are getting regular briefings on cyber, an average of two times per year across the entire board and four times per year at the committee responsible for cybersecurity,” says Lesley Ritter, senior vice president for Moody’s Investors Service.
“But the challenge remains whether the board has enough expertise to oversee cybersecurity,” adds Ritter. “The absence of relevant cybersecurity expertise makes it difficult for a board to effectively guide and oversee a robust, enterprise-wide cybersecurity risk management program.”
You’re a board member or CEO and you’ve read this report. Now what?
- Share this report with other members of the board and your C-suite executives. Then have a discussion about it at your next board meeting.
- Add cybersecurity experience to your board. This will help your board better understand cyber risk and your ability to mitigate that risk.
- Put a ransomware incident response plan in place that is approved by the board.
- Revisit your cybersecurity budget and be sure that it allows for swift action around unexpected cyberattacks and intrusions.
- Review your cyberinsurance policy and consider inviting your cyberinsurer to a board meeting to ensure your policy meets your needs.
- Put a succession plan in place for your CISO and consider initiatives to improve retention rates.
The Boardroom Cybersecurity 2023 Report provides boardroom and C-suite executives with cyber economic facts, figures, predictions and statistics that convey the magnitude of the cyber threat they are up against, and market data to help understand what can be done about it.
Chief information security officers (CISOs) are encouraged to borrow generously from our report when they enter the boardroom.
– Steve Morgan is founder and Editor-in-Chief at Cybersecurity Ventures. Charlie Osborne contributed..
SPONSORED BY SECUREWORKS
Secureworks (NASDAQ: SCWX) is a global cybersecurity leader that secures human progress with Secureworks® Taegis™, a SaaS-based, open XDR platform built on 20+ years of real-world detection data, security operations expertise, and threat intelligence and research. Taegis is embedded in the security operations of over 4,000 organizations around the world who use its advanced, AI-driven capabilities to detect advanced threats, streamline and collaborate on investigations, and automate the right actions.


 –
–