13 May Alert Fatigue: The Enemy Within Cybersecurity Professionals
Unburden your SecOps team with these best practices
Denver, Colo. – May 13, 2022
It’s tempting to throw money at cybersecurity solutions and invest in many different tools to protect ourselves. But these contrasting security products can generate a high volume of repetitive, low-fidelity alerts. This creates a growing internal enemy that threatens our ability to combat our external enemies: alert fatigue.
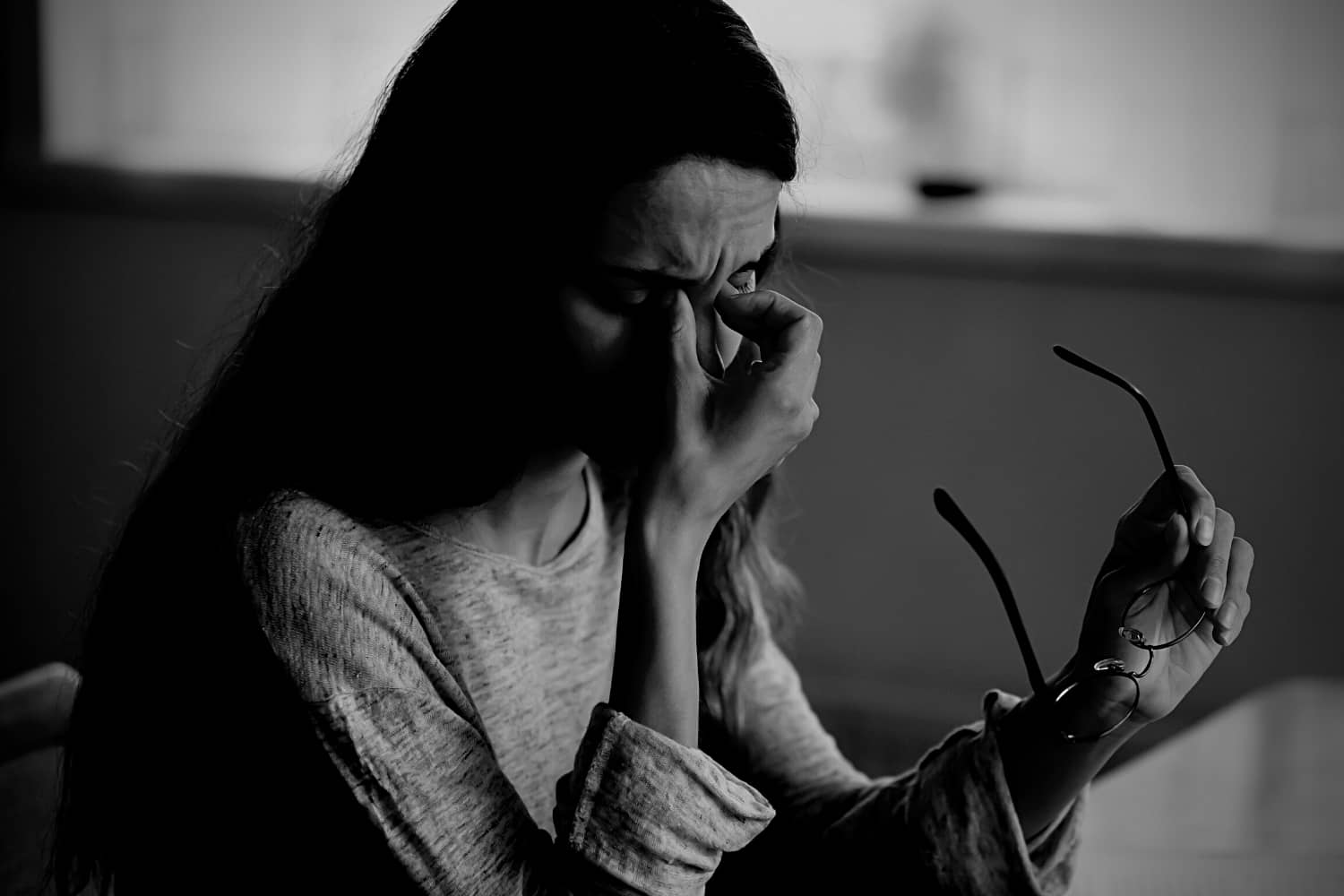
What is alert fatigue? It’s a seemingly uphill battle for cybersecurity professionals, one they fight every day. We’re simply overwhelmed by the sheer number of alerts on our screens. And it’s not just too many false positives. We’re also being inundated with alerts that are true positives but are of minor importance. These constant alerts can distract us from events that genuinely warrant immediate attention.
And make no mistake: alert fatigue is a true enemy. According to IDC, every alert we act upon costs about 30 minutes of our time. False positives take even longer to act on precisely because they are dead ends.
Excessive alert volume also increases the probability that something dangerous will slip through. IDC estimates that cybersecurity teams at companies with 5,000+ employees wind up ignoring about 23 percent of their alerts. At companies with 1,500-4,999 employees, that figure is more like 30 percent. Just as problematically, when the noise overwhelms the signal, you and your team can start to burn out and lose focus. You can even start unconsciously believing that your job is to clear alerts, rather than to protect your company.
As with so many other stress factors in our modern lives, our response to alert fatigue is often a little mitigation and a lot of resigned acceptance.
But the dynamics of cybersecurity require us to do more. Our external enemies — and the occasional malicious insider — keep attacking us with greater intensity. And while our budgets may be growing, they’re not growing at the same pace as that attack intensity. Plus, it’s hard to find, recruit, retain, and train cybersecurity talent.
We can’t afford to waste our time or allow our productivity to erode. So, what’s to be done?
The Alert Fatigue To-Do List
As attack volume increases — and as we deploy more technologically sophisticated sensors that give us earlier warnings about potential security breaches — alert fatigue, left untreated, will only get worse. That’s why it’s essential to aggressively apply the entire range of anti-fatigue best practices to your security operation.
Those best practices include:
- Take alert fatigue seriously. Because SecOps leaders focus so much on core tasks such as threat intelligence and threat hunting, it’s easy to get lax about addressing alert fatigue. But alert fatigue won’t go away by itself — and it poses a serious threat to SecOps effectiveness. So first and foremost, SecOps leaders must commit to making alert fatigue a top priority.
- Tuned suppression. It’s well worth investing the time necessary to fine-tune your cybersecurity tools so you can keep trivial and innocuous alerts off your team’s screens. You must be careful not to suppress any meaningful alerts in the process, but with a bit of effort you should be able to eliminate a lot of chaff without touching the wheat.
- Prioritized triage. Alerts will be a lot less fatiguing when your team can immediately see the specific information they need for rapid triage rather than the mouse, keyboard, and eyeball labor that’s needed just to decide whether a given alert is worth addressing immediately. Alerts that have been automatically validated and prioritized tell you with high confidence which are most critical and can help SecOps teams focus.
- Drill-down by design. The more alert-related data you suppress or de-prioritize, the more important it is that you make it as easy as possible for your team to drill down to the next level of data when they decide to investigate more deeply. And don’t rely on your vendors alone to determine what that next level of drill-down data should be. Make sure it just takes a few clicks for everyone to access the information they need to understand the true nature and context of any alert they choose to examine.
- Logical aggregation. A single issue can generate dozens of alerts. By aggregating related alerts, you reduce your total volume significantly. Your team will also be able to work through alerts much more quickly, intuitively associating new alerts with previous historical alert groups.
- “Top Ten” lists. You can also aggregate alerts by implementing “Top Ten” listings — by source IP, target IP and user, and other relevant attributes — on everyone’s primary dashboard.
- Bulk actions. You can save your team a lot of time and mental energy if you give them the ability to act on logical groups of alerts by performing bulk actions on them — such as moving them all to an open investigation collectively, rather than one at a time.
How Are You Doing?
There’s one more best practice to put on your list if you genuinely want to prevent alert fatigue from exacerbating your organization’s already-significant cybersecurity risk: continuous measurement and improvement.
As a SecOps leader, it’s imperative that you regularly assess how well you and your team are managing your alert workloads. What percentage of the alerts showing up on your screens are low-severity notifications? How does that percentage compare to last quarter? Is your alert queue getting longer or shorter? Was there a recent spike in alerts? How big was it? How well did your team cope with it?
By periodically reviewing select KPIs like these, you can make fact-based decisions about alert management and resource allocation. Reviewing KPIs with your team can also serve as an antidote against burnout, which may be the most pernicious long-term consequence of alert fatigue. Reviews let them know you’re on their side, and they give everyone a chance to pat each other on the back for any success they’ve achieved.
The bottom line: alert fatigue isn’t a fact of life. Get out your sword and slay it! Your team’s mental health – and your ability to effectively protect your organization – depend on it.
– Steve Snyder is Director of Portfolio Marketing at Secureworks
About Secureworks
Secureworks is 100 percent focused on cybersecurity. In fact, it’s all we do. For nearly two decades, we’ve committed to fighting the adversaries in all their forms and ensuring that organizations like yours are protected.
Secureworks® Taegis™, a cloud-native security analytics platform built on 20+ years of real-world threat intelligence and research, improves your ability to detect advanced threats, streamline and collaborate on investigations, and automate the right actions.


 –
– 