28 Feb List Of Cybersecurity Books From The Editors at Cybercrime Magazine
Books that arm readers in the war against cybercrime

Northport, N.Y. – Apr. 5, 2023
Our editors are constantly pitched by authors on the latest and greatest cybersecurity books. But only a small percentage of them get a thumbs-up from us.
With only so much time to read, we aim to filter out the best books for our readers.
Cybercrime Magazine is excited to bring you video reviews on some of the classics, as well as brand new titles that are just hitting the shelves.
Scott Schober, our chief security officer, takes a deep dive into each book — and provides you with his authoritative opinion.
Cybercrime Radio: “Fancy Bear Goes Phishing”
New book on the history of hacking
VIDEO REVIEWS
If a book makes it onto our list, then it’s worth buying. But watch the video review and decide for yourself. We cover cybercrime, cybersecurity, cyberwarfare, digital privacy, and human interest stories.
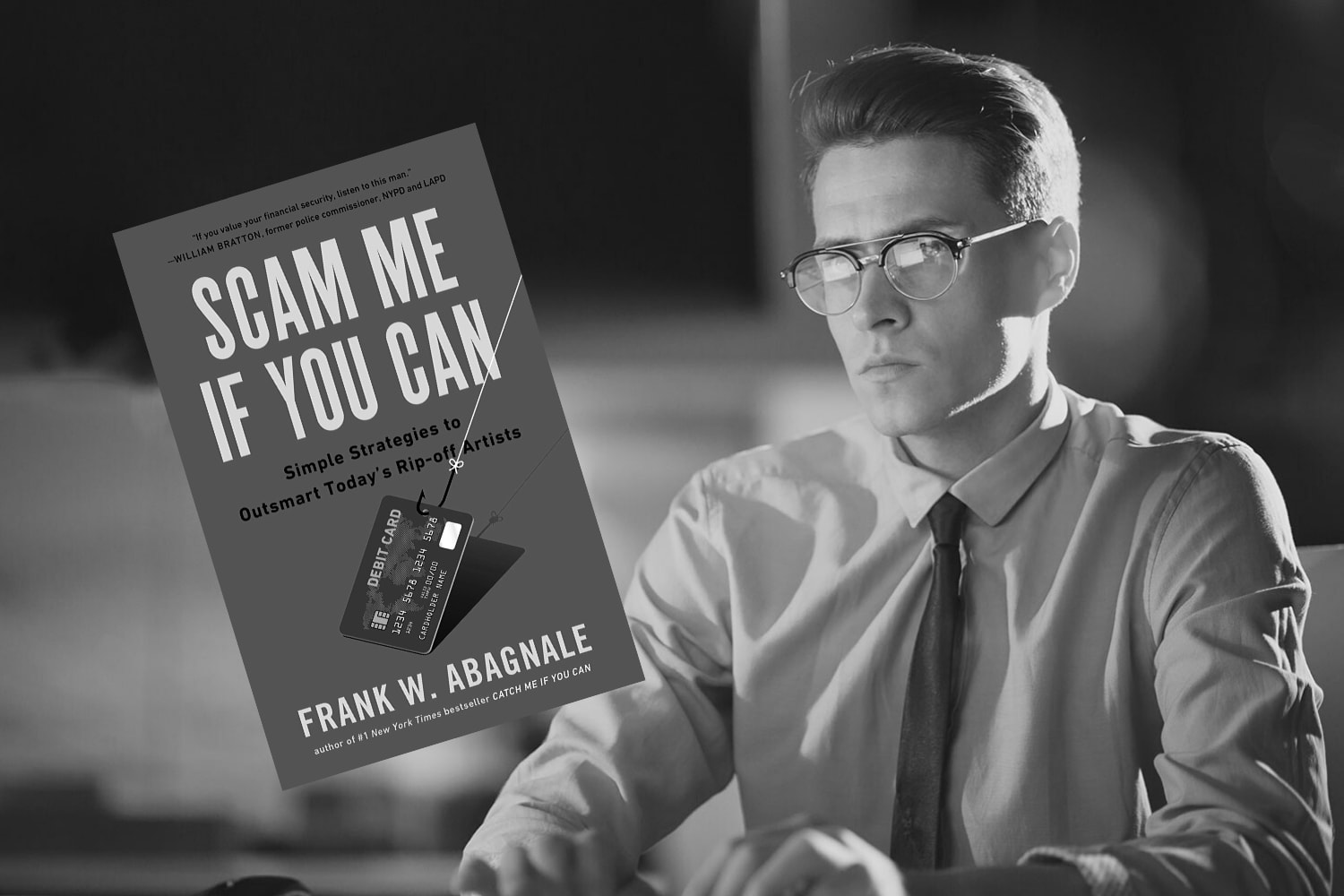
- Scam Me If You Can. Simple Strategies to Outsmart Today’s Rip-off Artists. Frank Abagnale. His story provided the inspiration for the 2002 film, Catch Me If You Can.
- Cybersecurity Is Everybody’s Business. Solve the Security Puzzle for Your Small Business and Home. Scott Schober. A wake-up call on modern cyber threats.
- Ghost in the Wires. My Adventures as the World’s Most Wanted Hacker. Kevin Mitnick. A must-read written by the world’s most famous hacker.
- Data and Goliath. The Hidden Battles to Collect Your Data and Control Your World. Bruce Schneier. The New York Times Bestseller from renowned cryptographer.
- Future Crimes. Inside the Digital Underground and the Battle for Our Connected World. Marc Goodman. The New York Times Bestseller from a digital futurist.
- The Art of Invincibility. The World’s Most Famous Hacker Teaches You How to Be Safe in the Age of Big Brother and Big Data. Kevin Mitnick. For citizens and consumers.
- Spam Nation. The Inside Story of Organized Cybercrime — from Global Epidemic to Your Front Door. Brian Krebs. Investigative journalist unmasks cybercriminal masterminds.
- Swiped. How to Protect Yourself in a World Full of Scammers, Phishers, and Identity Thieves. Adam Levin. Identity theft is a fact of life. Learn how to protect yourself.
- Women Know Cyber. 100 Fascinating Females Fighting Cybercrime. Steve Morgan and Di Freeze. Role models for anyone contemplating a career in cybersecurity.
- Manipulated. Inside the Cyberwar to Hijack Elections and Distort the Truth. Theresa Payton. Former White House CIO on how your beliefs are being meddled with.
100 BEST CYBERSECURITY BOOKS
As featured on CNN, Forbes and Inc. Magazine — BookAuthority identifies and rates the best books in the world, based on recommendations by thought leaders and experts.
In its list of “100 Best Cybersecurity Books of All Time,” BookAuthority features “Women Know Cyber,” published by Cybersecurity Ventures.
BookAuthority, the world’s leading site for book recommendations by thought leaders, identifies and rates the best books using dozens of different signals, including public mentions on social media, user ratings, popularity and sales history.
Only the very best books are featured on BookAuthority. To keep their site objective and unbiased, ratings are calculated purely based on data. They do not honor requests to feature books, nor are they getting any money from publishers or authors.
GET IN TOUCH
Is there a book you’d like us to review? Tell us about it.
Stay tuned for more book reviews!
– Steve Morgan is founder and Editor-in-Chief at Cybersecurity Ventures.
Go here to read all of my blogs and articles covering cybersecurity. Go here to send me story tips, feedback and suggestions.



